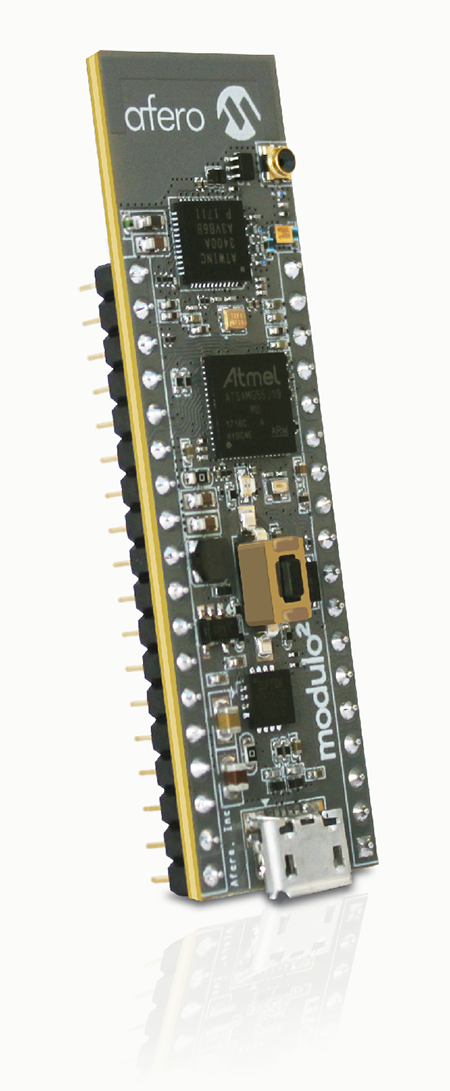
 The Modulo-2. Source: Afero
The Modulo-2. Source: Afero
Last October, as you may recall, a distributed denial-of-service (DDoS) attack last disrupted several major websites and highlighted the vulnerability of the internet’s domain name system (DNS) infrastructure. At the center of the attack were insecure internet of things (IoT) devices, also known as “smart” devices.
While a recently-introduced, bipartisan Congressional bill aims to establish industry-wide security practices, the pace of legislation can often be frustratingly slow. In response, Afero — a firm comprised of veterans from Apple, Google, Nest and other tech industry giants — has developed and patented encryption and authentication technologies that represent a multi-layered and proactive approach to IoT security.
The company announced today the launch of an IoT development kit designed to give developers the equivalent of an ultra-secure virtual private network (VPN) for building devices. According to a press release, the Afero Modulo-2 can fast-track the prototyping and production of connected devices in up to 50 percent less time. Afero has partnered with semiconductor manufacturer Microchip Technology to make the kit available worldwide through the online sales channel microchipDIRECT.
Afero says that the Modulo-2 kit provides hardened edge-to-cloud security, easy device on-boarding, powerful over-the-air (OTA) update management, and tools and code for prototyping through production. Its compact form factor contains Microchip hardware, including a microcontroller (SAM G55), secure element (ECC508A), and combination Wi-Fi and Bluetooth low energy integrated circuit (WINC3400) that enables secure, low-energy connectivity to the Afero IoT Platform. The kit can be used on any Microchip development board with an Xplained Pro (XPRO) interface.
Features of the Afero managed security approach include: cryptographic enforcement of authorized communication between edge device and cloud; forward secrecy; secure cloud-based policy controls; and cryptographically-valid data and connection security that extends all the way to the device manufacturer. Also supported are continuous, round-the-clock monitoring of background behavior and IoT-specific countermeasures to defend against attacks.
For detailed developer information, visit the Afero Developer Portal.

