Connected medical devices are big business these days, providing remote care solutions for a variety of healthcare needs. A recent estimate by Berg Insight puts the number of remotely-monitored patients worldwide at 7.1 million — and predicts that this number will reach a staggering 50.2 million by the year 2021. There are many positives to this trend, including increased efficiency, lowered costs and improved patient care. But there’s another aspect to this kind of connectivity as well — vulnerability.
As reported on the information security site Help Net Security, research conducted in 2017 by IoT security provider Zingbox on tens of thousands of connected medical devices uncovered a wide range of vulnerabilities. The most common type, accounting for 41 percent of all issues, came from security compromises that users introduced themselves — things like using browsers embedded on medical workstations to visit risky websites or download content. Ranking second, at 33 percent, was devices running outdated operating systems or software.
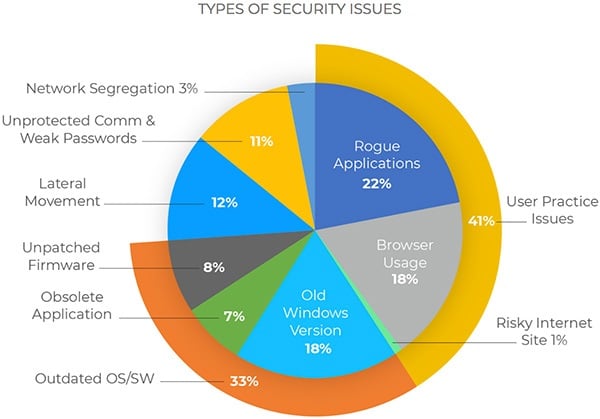 Breakdown of security issue types from 2017 Zingbox study. Source: Zingbox.While these may seem like small infractions, Zingbox notes that the threat posed by vulnerabilities in the system is hardly insignificant. There is a growing number of attacks aiming to disrupt an organization’s ability to provide care, in addition to the ongoing threat of attacks aimed at stealing personal health information. In 2016, according to The Atlantic, nearly nine out of every 10 ransomware infections targeted a healthcare provider.
Breakdown of security issue types from 2017 Zingbox study. Source: Zingbox.While these may seem like small infractions, Zingbox notes that the threat posed by vulnerabilities in the system is hardly insignificant. There is a growing number of attacks aiming to disrupt an organization’s ability to provide care, in addition to the ongoing threat of attacks aimed at stealing personal health information. In 2016, according to The Atlantic, nearly nine out of every 10 ransomware infections targeted a healthcare provider.
In terms of actionable insight to guard against vulnerabilities, Zingbox points to the importance of knowing the type of device involved. For instance, infusion pumps (e.g., insulin pumps) have an average of just one network application, which is internal to the organization’s network. Despite the fact that they represent the most common type of device in the study, infusion pumps are among the lowest offender in terms of security issues. Imaging systems like X-ray, ultrasound and MRI machines, by contrast, are characterized by a particularly high number of network applications — an average of seven, including an average of three used for communications outside the organization. They also are often designed on commercial off-the-shelf operating systems, are expected to have long lifespans and are very expensive to replace. All of these factors contribute to imaging systems having highest percent of security issues.
However, older devices, regardless of type, are more vulnerable to newly emergent security threats. In some cases, these “legacy” devices are being used as connected devices despite never having been designed as such. For instance, a device might have a USB port originally meant for software upgrades — that port might get used to connect to a hospital network, or to upload malicious software. IoT security provider Attify notes that security has largely been an afterthought in the rush to connect medical devices. Thanks to devices being set up by various vendors in different hospital departments, adds healthcare cybersecurity firm secureHIM Inc., administrators may not even have a clear picture of all the devices on their networks.
 Infusion pumps like this one are among the most common types of connected devices.In September 2017, the U.S. Department of Homeland Security issued a detailed warning about vulnerabilities in a certain brand of infusion pump — not the type of device one might normally expect to be affected. Intended for delivering small doses of medication in acute care settings, the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) warned that the vulnerabilities could be exploited by a remote attacker in order to gain unauthorized access and impact the pump’s intended operation. The maker of the pump responded with recommendations for defensive measures, including the deployment of virtual local area networks (VLANs) for segmentation — this, along with a consideration of network micro-segmentation, is one of the top recommendations from numerous cybersecurity experts.
Infusion pumps like this one are among the most common types of connected devices.In September 2017, the U.S. Department of Homeland Security issued a detailed warning about vulnerabilities in a certain brand of infusion pump — not the type of device one might normally expect to be affected. Intended for delivering small doses of medication in acute care settings, the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) warned that the vulnerabilities could be exploited by a remote attacker in order to gain unauthorized access and impact the pump’s intended operation. The maker of the pump responded with recommendations for defensive measures, including the deployment of virtual local area networks (VLANs) for segmentation — this, along with a consideration of network micro-segmentation, is one of the top recommendations from numerous cybersecurity experts.
There are some bright developments to report — a bill introduced in the U.S. Senate would increase medical device transparency by creating a “cyber report card” for devices, requiring testing to be performed before devices could be sold. The U.S. Food and Drug Administration (FDA) has issued a guidance document that describes the necessary risk analysis for pre-market review, and the agency is also performing surveillance in the post-market phase to help companies figure out how to reassess their cybersecurity measures. And a 2017 report by the Health Care Industry Cybersecurity Task Force, a public/private partnership established by the U.S. Congress, outlines a comprehensive approach to address healthcare cybersecurity — albeit after concluding that its current state is one of “critical condition.”


