As increasing numbers of companies move to the cloud and software-as-a-service (SaaS) applications continue to increase the flexibility employees have to be able to work from anywhere, businesses are recognizing the 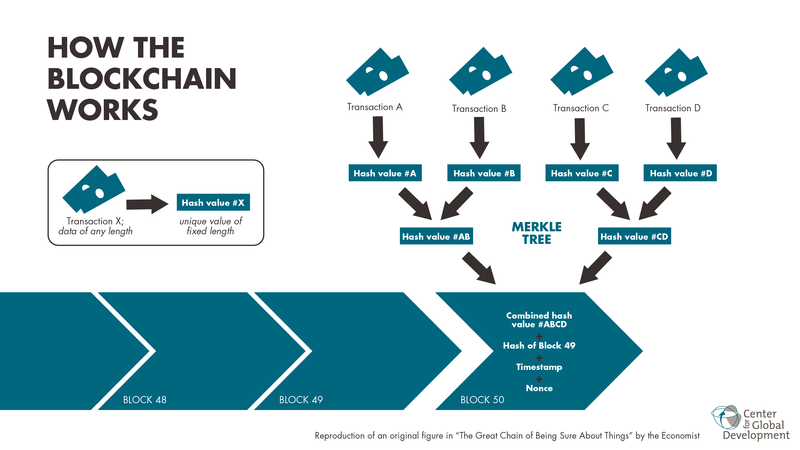 Source: B140970324 / CC BY-SA 4.0importance of security. Swapping desktops for internet browsers means consuming more cloud services, and IT must move toward providing a secure digital workspace platform while providing users with a more personalized work experience.
Source: B140970324 / CC BY-SA 4.0importance of security. Swapping desktops for internet browsers means consuming more cloud services, and IT must move toward providing a secure digital workspace platform while providing users with a more personalized work experience.
Here are three things IT executives must acknowledge while constructing a successful security strategy.
Insiders are one of the biggest threats. Actions by disgruntled or untrained employees — whether purposeful or accidental — can have catastrophic consequences. In the case of intentional data theft, the crime can go unnoticed for months or even years. Take Alphabet, Google’s parent company, which in April filed a lawsuit against its former engineer Anthony Levandowski, who is now at rideshare company Uber. Alphabet alleges Levandowski had copied more than 14,000 internal files and is sharing them with Uber. The situation is more common than many companies acknowledge: The Ponemon Institute looked at 874 incidents, and found that 568 were caused by employee or contractor negligence and 191 by malicious employees and criminals. Only 85 were caused by outsiders using stolen credentials. In 2018, organizations will place more focus on insider access to avoid security breaches.
Analytics will help batten down the hatches. Businesses often use multiple security products such as security information and event management tools (SIEMs), antivirus software and data loss prevention tools. Ironically, those solutions generate huge amounts of data, which can hide the critical information that requires immediate attention. Still, to understand what is going on in a business, organizations need advanced analytics tools that can process data from multiple sources and environments and identify the potential activities that could pose a threat to sensitive data. Technologies such as user and entity behavior analytics (UEBA) help organizations establish tighter control over their IT infrastructures and gain an understanding of their weak points, so they can patch security holes before a data breach occurs and determine what areas will likely need attention ahead of a disaster.
Blockchain is not just for cryptocurrency. It’s appropriate that a technology employed in moving currency around the Web could be used for locking down IT security systems. Blockchain could become a major security technology: It allows information to be stored in a decentralized and distributed manner, rather than as a large target. Rather than residing in one location, data is stored as an open-source ledger. It is a series of blocks that records time-stamped data in hash functions. Any change in the ledger is noticed by those participating in the chain, a strategy that can prevent data hacking and tampering. Because the stored information can’t be overwritten, data manipulation is extremely impractical.
Organizations have their own IT pain points, and while they may seem painfully unique to each, similarities are often shared by other businesses. Companies are in good company, and as a result, have strength in numbers as they together become more active about securing confidential data. Those with bad intent in 2018 will find it will take more time and effort to access and steal corporate data, and that, coupled with better technology solutions, is a powerful deterrent.

