There will be nearly 6.2 billion Internet-enabled devices manufactured this year, according to IHS Technology, a 6% increase over last year. But how secure will those devices be, and how high up on OEMs’ priority lists is preventing malicious attacks from invading their Internet of Things (IoT) products?
Unfortunately, not high enough, say experts. And, they add, the demand for “smart” devices that combine sensors, connectivity, and embedded processing capabilities depends on user acceptance. This acceptance, in turn, relies on calming consumers’ fears about lack of privacy and security. So, the experts warn, OEMs ought to be stepping up their security risk assessments.
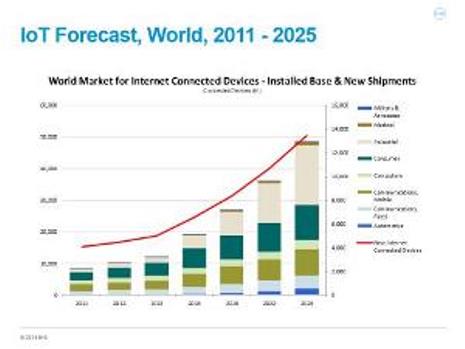
Source: IHS
“Sadly, up until recently, security in IoT has been a bit like security in the retail POS industry, where it’s done more on a ‘good enough’ basis than on a worst-case-scenario basis,” says Bill Morelli, associate director, Internet of Things, at IHS. “It was more about what’s the minimum we need to do to get by, to make people reasonably comfortable, and then we’ll absorb any loss above that.”
However, that seems to be changing, observes Morelli, because consumer confidence has been shaken by some very high-profile breaches that are causing OEMs to pay more attention than they had previously.
“But is it enough?” he asks. “There’s probably still more OEMs can do, frankly.”
Especially, he adds, in the areas where technology and connectivity are advancing the fastest, like in smart homes, smart buildings, and connected automobiles. Although there hasn’t been an abundance of security malfeasance in those arenas, that doesn’t mean the bad guys aren’t testing the waters.
In January, Sunnyvale, CA-based Proofpoint uncovered what it says may be the first proven IoT-based cyberattack involving conventional household smart appliances. The security-as-a-service provider identified over 750,000 malicious e-mail communications coming from more than 100,000 everyday consumer gadgets, such as home-networking routers, connected multimedia centers, TVs, and at least one refrigerator that had been compromised and used as a platform to launch attacks.
Morelli expects to see far more as consumer interest in IoT explodes.
“Apple computers never used to be a target of malicious activity either, until they became popular,” he explains. “Hackers only used to go after the Windows computers because they were the huge market of low-hanging fruit. Similarly, as more and more consumers decide that it’s really cool to control the door locks on their homes with their smartphones, you can be sure smart locks, for example, will become a bigger target than they are now.”
Two companies that build vastly different IoT security products concur. One is Aliso Viejo, CA-based Microsemi which takes a hardware approach, manufacturing a secure field-programmable gate array (FPGA) designed to ensure that processors and systems boot securely.
Many engineers design on a very short schedule and a very tight budget, which is why they primarily design to functional requirements, says Tim Morin, director of product line marketing at Microsemi. “That means they may not have time for a security risk assessment and they are not necessarily concerned about when their system communicates with an outside system, whether some sort of mutual authentication scheme exists.”
His suggestion to OEMs is to make certain that the processors and systems in their products boot securely. Otherwise, he says, an unreliable and untrusted system exists.
Microsemi’s two products – the SmartFusion2 SoC FPGA and the IGLOO2 FPGA – are both designed with security in mind. Specifically, the company describes them as the only FPGAs available that come equipped with a random number generator, a physically cloning-proof function (licensed from Intrinsic ID), an elliptical curve cryptography core, and a differential power analysis (DPA) license from Cryptography Research.
“We offer on-chip flash inside a secure FPGA so the only way you can write to the device is with an encrypted authenticated bitstream,” says Morin.
In addition, Microsemi can provide customers with a reference design that can help thwart the installation of malicious rootkits.
In comparison to Microsemi’s hardware approach, a second company focused on IoT security, Edmonds, WA-based wolfSSL, provides OEMs with its CyaSSL software, an open-source SSL programming library built in the C language that’s targeted for use by embedded systems developers.
“Frequently, these embedded IoT devices are very resource-constrained and developers have to make tradeoffs between a higher feature set and the correct security level that ought to be in place, especially when they are really in a hurry to rush their products to market,” says Chris Conlon, a software engineer at wolfSSL. “In addition, by the nature of embedded devices, they are sometimes less secure because they don’t necessarily have regular firmware updates or patches once they’ve been distributed.”
He encourages engineers to design with security in mind from the ground up instead of designing devices first and then layering security on top as an afterthought.
“It’s also a good idea to standardize on some kind of common security protocols or common framework,” he says, “as well as to use strong cryptography and to provide secure firmware updates.”
IHS’ Morelli has a few more suggestions for security-minded OEMs:
- Don’t build your products with default security settings. When consumers unpack or set up the system, force them to select and input a user name and password. Currently the situation is reminiscent of when router manufacturers used to allow consumers to retain the default settings to simplify setup, which made hacking into the system a snap.
- Work closely with your partners to explore and install more robust security solutions. Determine the appropriate amount of security for the particular device and enable it using hardware or software.
Looking ahead, Morelli predicts the future will embrace multi-factor authentication, not just a password but also a “physical token,” like a smartphone or a keychain.
“There’s been a lot of discussion about using consumers’ smartphones as their security keys to all of their cloud services, all their connected devices, to their home or office, and to their vehicle devices, because the phone contains a SIM card which is one of the most secure locations on the planet,” he says.
“Further down the road, you’re going to see OEMs adopting biometrics as an additional part of a multi-factor authentication system,” Morelli adds. “It’s still an expensive solution, and some biometrics work better than others, but when the technology improves, I predict that’s the direction security-minded manufacturers will take.”
Related Articles:

