 IC fabrication processes create slight variations in each chip, creating “silicon biometrics.” Developers are using these physical unclonable functions to enable IC-level authentication and key generation features. Image source: Verayo. PUFs mark a shift to a security approach in which hardware plays a major role, providing the means to implement a scalable security scheme that extends down to the IC level.
IC fabrication processes create slight variations in each chip, creating “silicon biometrics.” Developers are using these physical unclonable functions to enable IC-level authentication and key generation features. Image source: Verayo. PUFs mark a shift to a security approach in which hardware plays a major role, providing the means to implement a scalable security scheme that extends down to the IC level.
These changes represent a major transformation in the way security is perceived and implemented. The question is: what forces triggered this shift and propelled PUFs to the forefront? Also, what makes this technology so relevant now?
The IoT Changes Everything
The answer to these questions can be found in the emergence of the Internet of Things (IoT) and distributed infrastructure paradigms like fog computing. These technologies link devices and systems to the internet that previously were isolated—either partially or completely—from the outside world. As sensors, actuators and machines become better connected to the broader network, operators can no longer depend on physical isolation to ensure networked devices’ security.
“I’ve always said that the rise of the IoT is a ‘monolithic moment’ in the evolution of computing,” says Tom Luczak, co-founder and chief technology officer of Flow Corporation. “Every organization, software developer and electrical engineer now has the ability to not only capture myriad aspects of their physical world and operations, but also to effect change in them as well—and at a scale never before seen. This is a tremendous opportunity, and a tremendous risk.”
The changes triggered by these networking paradigms, however, go beyond simply exposing new elements to security risks. Increasingly, communications will occur between semi-autonomous systems that range in size and complexity from simple embedded systems to larger devices. In addition, the scale of the communications will increase dramatically, as the network begins to accommodate the billions of “smart” objects expected to populate the IoT.
When you look at the emerging network landscape from a traditional IT perspective—where the authentication and access-control processes are based on credentials supplied at least in part by humans—the idea of assimilating thousands of semi-autonomous devices into a walled garden can be daunting.
In some cases, the same techniques for securing IT systems today can be applied to large distributed systems, but with a few new twists. Just as biometrics can use unique physiology traits to identify a human, PUFs can use silicon features to positively identify hardware and initiate cryptographic communications. Think of these features as silicon fingerprints.
Silicon Biometrics
At its core, a PUF is a variability-aware circuit that can detect unique properties in circuit components caused by variations in the characteristics of silicon hardware of a specific device or chip. These characteristics arise from unreproducible process irregularities that occur during the manufacture of the chip, such as randomness in dopant distributions, line-edge roughness and variations in gate oxide thickness. These silicon variations lead to small differences in the electrical properties of transistors—such as gain factor and threshold voltage—but they do not affect the normal operation of the chip. PUFs measure these variations, using them to identify the unique fingerprint of every silicon device.
Technology providers can measure these variations in two ways. In the first approach, the designer constructs dedicated asynchronous circuits with specific transistor architectures that detect variations in silicon properties. For example, this can be done with circuits that detect variations in the delay of circuit paths. Ring-oscillator PUFs and arbiter PUFs are examples of this approach.
The second approach leverages existing circuit components, such as on-chip memory. A good example of this approach would be the use of a standard six-transistor SRAM, the kind that can be found in almost every chip. The symmetric design of the SRAM cell leads to a natural amplification of transistor differences when the SRAM cell is powered up. Silicon variations can simply be measured by reading out the start-up values of the uninitialized memory. Every individual SRAM cell has a preferred start-up state of 0 or 1, which is determined by the relative variation in transistor threshold voltages. For a block of SRAM cells, this leads to a pattern unique for every chip.
“This approach clearly has many practical advantages,” says Geert-Jan Schrijen, chief technology officer of Intrinsic-ID. “By reusing a component that is available by default, no specific test runs are needed in the manufacturing process to tune the measurement circuit (as is the case with the second approach). Moreover this approach also works on existing silicon, which allows for retrofitting security onto devices already in the field by updating their software.”
PUFs in Action
Design engineers can implement PUFs to enable a variety of security features. Chief among these are device authentication and key generation and storage.
To confirm a device’s right to interact with services, the PUF initiates authentication with a challenge–response process, where a physical stimulus is applied to the silicon structure. The silicon reacts in a unique but repeatable way as a result of the complex interaction between the stimulus and the silicon hardware. The applied stimulus is called the challenge, and the reaction detected by the PUF is the response. A specific challenge and its corresponding response together form a challenge–response pair (CRP). The PUF uses the variations in the characteristics of silicon hardware to establish the device's identity. Stored CRPs can later be used to authenticate the device remotely with a challenge–response protocol, where a challenge is sent to the device and the response is verified with the previously recorded response.
This process, however, requires the designer to compensate for a security weakness emanating from its need for a so-called strong PUF, which supports a large number of independent CRPs. “Strong PUFs are subject to machine-learning attacks if the responses to too many challenges are exposed, so there needs to be a lockdown mechanism to prevent arbitrary access,” says Mandel Yu, chief scientist at Verayo. “One way this can be achieved is by using strong PUFs to provide mutual authentication so that the PUF device would respond only to the correct server.”
Another approach uses the silicon fingerprint to generate security keys, which can be stored and used later.
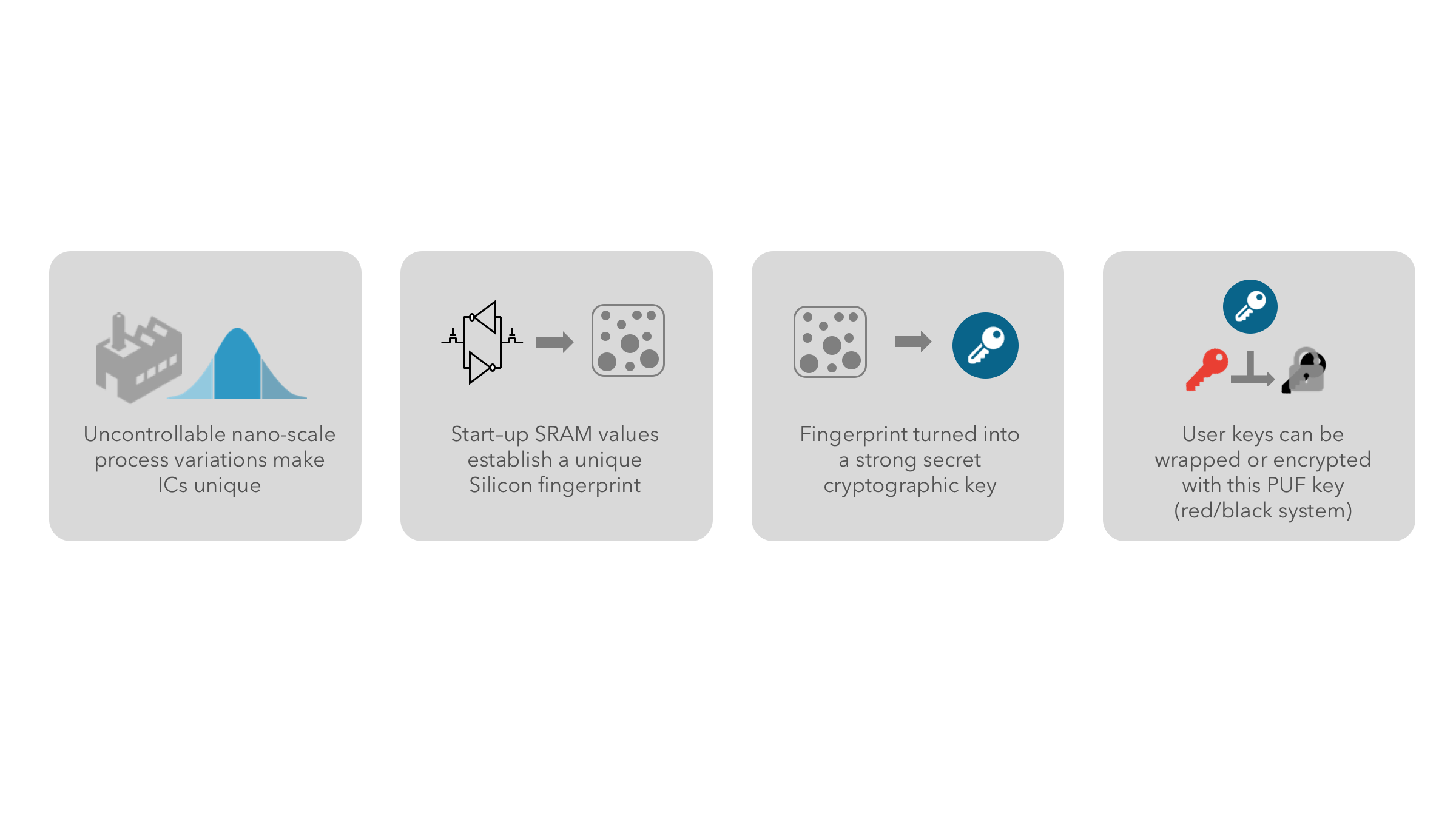 Variations created in the silicon during the manufacturing process define the start-up values of a static random-access memory (SRAM) cell. An SRAM PUF uses those values to derive a device-unique cryptographic key. The PUF key is typically used to wrap (encrypt and authenticate) other keys needed by the device to interact with services. Image source: Intrinsic-ID.
Variations created in the silicon during the manufacturing process define the start-up values of a static random-access memory (SRAM) cell. An SRAM PUF uses those values to derive a device-unique cryptographic key. The PUF key is typically used to wrap (encrypt and authenticate) other keys needed by the device to interact with services. Image source: Intrinsic-ID.
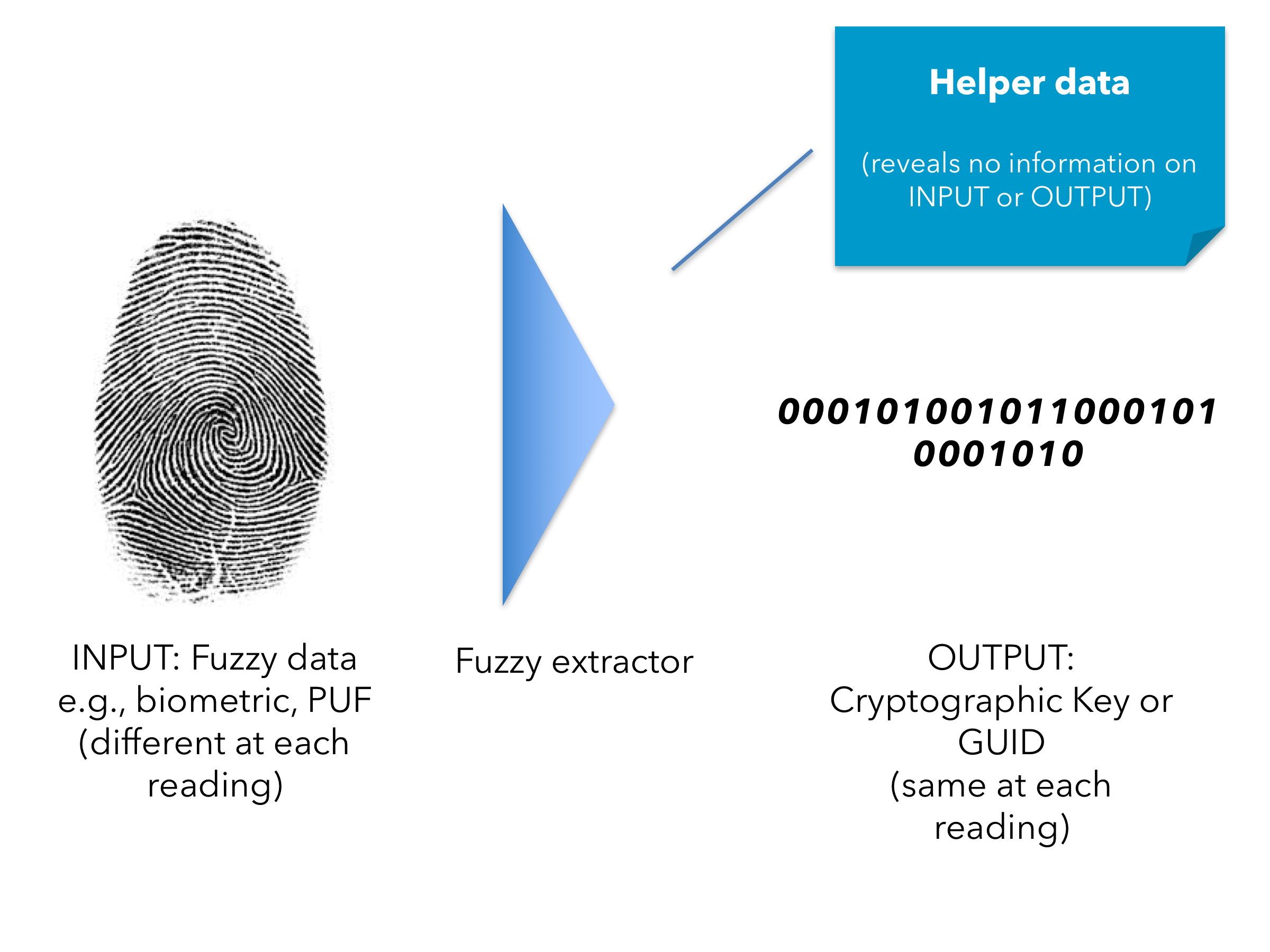
Because of the noise present in the fingerprint, generating a key requires error correction and entropy extraction. Error correction makes sure that the same key is reconstructed every time, under all environmental conditions. This is done by applying error-correcting codes. Entropy extraction ensures that the pattern results in a fixed-length (e.g., 256 bits), uniformly distributed pattern of bits. Both these steps are implemented in a fuzzy, or key, extractor.
 Variations created in the silicon during the manufacturing process define the start-up values of a static random-access memory (SRAM) cell. An SRAM PUF uses those values to derive a device-unique cryptographic key. The PUF key is typically used to wrap (encrypt and authenticate) other keys needed by the device to interact with services. Image source: Intrinsic-ID.
Variations created in the silicon during the manufacturing process define the start-up values of a static random-access memory (SRAM) cell. An SRAM PUF uses those values to derive a device-unique cryptographic key. The PUF key is typically used to wrap (encrypt and authenticate) other keys needed by the device to interact with services. Image source: Intrinsic-ID.
This approach provides a reliable device-unique key derived from the characteristics of the silicon. The key is typically used to wrap (encrypt and authenticate) other keys needed by the device to interact with services. The wrapped keys can be stored in non-secure memory, and they are unwrapped only when needed by the application running on the device. This approach fits seamlessly with existing symmetric and asymmetric authentication protocols.
The Right Place at the Right Time
While PUF technology has been around in one form or another for almost 10 years, the silicon-level security has finally begun to come into its own with the emergence of the IoT and networking paradigms like fog computing. These forces have triggered an explosion in the number of networked devices and network interactions, and as a result, the industry has seen a corresponding increase in security threats. All these factors have come together to create demand for inexpensive, energy-efficient and scalable security technology, and that is just what PUF-based systems deliver. PUFs have arrived at the right place, at the right time, with the right functionality, and therein lies the relevance of the technology.
The beauty of PUF-based security resides in its physical nature. The unique silicon attributes at the core of the technology are random, repeatable and elusive. No one can duplicate or imitate the hardware features. In addition, PUF security modules are small enough to be embedded in a variety of devices, ranging from sensors and processors to wearable devices, and PUF-based key generation mechanisms easily integrate into any ASIC and FPGA.
Essentially PUFs reduce the window of opportunity for an attack, which is where traditional security measures fall short. “Conventional technology can be attacked when powered off,” says Yu. “PUF secrets are present only during the fraction of time when the secrets are used on chip, and are therefore more difficult to attack. Conventional technologies store secret bits in a persistent, non-volatile manner. PUF-generated keys disappear when the device is powered off. If secret bits are persistent even when not being used, they are easier to discover through physical attack.”
Moving Forward
Despite its maturity, PUF technology still has room for improvement. Continuing work on the basic PUF technology will lead to optimization in terms of footprint, speed, code size and SRAM usage.
Although SRAM PUF will probably remain a key aspect of the technology in the coming years, research on other PUF types will evolve as well. “New memory types such as resistive RAM will provide new opportunities for creating PUFs,” says Schrijen. “It will take several years, though, before these new memories are common and become a practical replacement for the widely available SRAM PUF."
On the flip side, the technology’s biggest challenge may well turn out to be public perception and awareness. “Security is a key concern for most developers, and the landscape is changing at a rate that it is hard to keep up with,” says Angela Raucher, product line manager at Synopsys. “It could be easy to overlook technologies that could solve system challenges.”
The inertia in the marketplace has to be addressed and overcome by shedding light on the capabilities of PUF technology. But before this can happen, technology developers and consumers will have to adopt a new security mindset.

